In today’s digital age, your smartphone, like your iPhone, is more than just a fancy gadget; it’s an extension of you. It contains crucial information, including your personal photos, emails, contacts, and even financial details. Therefore, it’s essential to keep it secure and ensure it hasn’t been tampered with for your peace of mind and protection of data. Furthermore, unauthorized opening of your iPhone can lead not only to loss of warranty but also potential damage to the delicate internal components. Consequently, learning how to check if your iPhone has not been opened plays a paramount role in maintaining your cybersecurity hygiene and overall device integrity.
Identification of iPhone Tamper-evidence Features
Apple takes data privacy and security very seriously. The company has invested significantly in making the iPhone design tamper-evident. Understanding what an untouched iPhone looks like and the importance of tamper seals and screws will help in confirming if your device has been interfered with.
Internally, iPhones are developed with clearly visible red strips that turn pink or red when they come in contact with water; this is known as liquid contact indicators (LCI). They are employed to check instances of water damage—one of the main reasons for iPhone breakdowns. Spotting this color change could signify possible device opening.

Detailed Step-by-step Guidance on How to Check if Your iPhone Has Not Been Opened
Checking if your iPhone has been opened involves observation, software checks, and functionality tests.
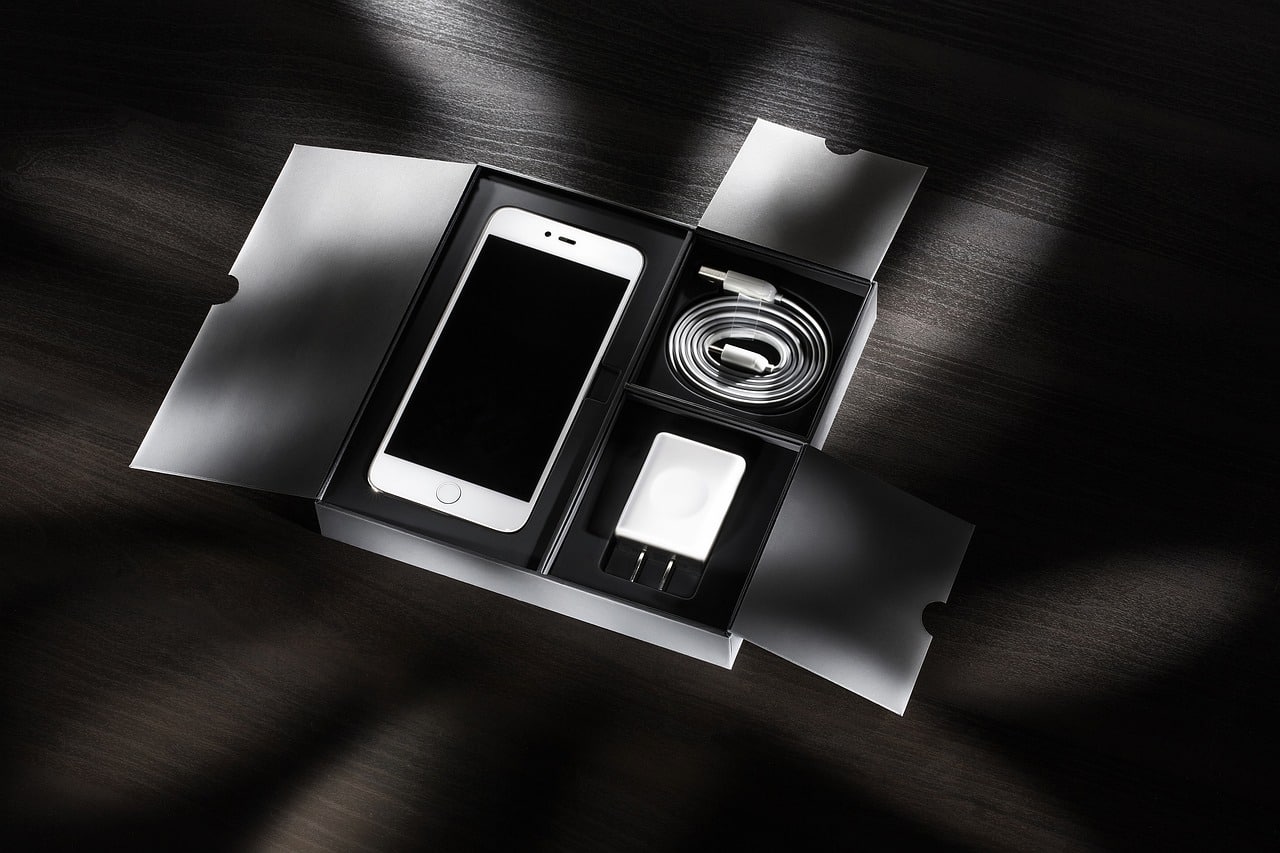
Firstly, scrutinize the iPhone’s external condition. Look for any signs of manipulation, scratches, mismatched colors or replaced parts.
Secondly, consider the tampering screws found at the bottom of the device next to the charging port. Apple uses specialized five-pointed pentalobe screws, which are impossible to open with commonly available tools.
Next, check for any unusual behavior within the iPhone’s iOS software. Sluggish performance, frequent crashes, or unusual pop-ups could hint at unauthorized modifications.
Lastly, test the functioning of various hardware like the buttons, touch screen, speakers, mics, and cameras. Any malfunction could suggest internal tampering.
Methods to Detect Signs of Third-party Opening
In the digital age, safeguarding our personal devices against unauthorized access is a crucial concern. Detecting third-party interference with your device, particularly an iPhone, requires meticulous observation and a bit of know-how.
Checking for Part Replacements
One of the initial steps in identifying if your iPhone has been compromised is to examine it for any part replacements. Components not furnished by the original manufacturer may be easily identifiable. These could differ in color, texture, or how they function compared to the authentic parts. A mismatch in the quality and design of the screen, buttons, or even the back casing can be telltale signs of third-party interference.
Monitoring for Unofficial Software Modifications
Another red flag can be the presence of unfamiliar software changes. Unofficial or unauthorized software may introduce strange icons, unexpected apps, or unusual settings that were not originally part of your device’s ecosystem. These modifications could potentially indicate that someone has tampered with your device’s software.
Looking for Missing Screws or Seals
Physical inspection of your iPhone is equally important. Check for missing screws or tampering with security seals which are designed to indicate whether a device has been opened. If screws are missing or if parts within the phone seem loose or out of place, it is plausible that the phone has been dismantled by someone other than an authorized service provider.
Inspecting for Data Irregularities or Missing Data
Finally, scrutinizing the data stored on your device is crucial. An unexpected loss of data or unfamiliar configuration changes can suggest that your phone has undergone some form of unauthorized tampering. Such data irregularities can also be symptomatic of malicious software or third-party interventions aiming to extract personal information.
Instances When Your iPhone Could Potentially be Opened
Your iPhone may be vulnerable to unauthorized openings in several situations. Recognizing these can assist you in taking proactive steps to secure your device.
Situations Leading to Unauthorized Openings
Often, the risk of third-party access arises when you hand over your iPhone for repair or when you decide to sell it. During repairs, there’s always a possibility of your device being opened by someone other than certified technicians, especially if you choose a non-authorized service provider. Similarly, when selling your device, the new owners or intermediaries might open the device for various reasons without your consent.
Understanding Unauthorized Openings and Risks
Comprehending the motivations behind unauthorized openings and associated risks is vital. Such intrusions could be for benign purposes such as repairs, but they could also involve malicious intent such as espionage or data theft. Understanding these risks is the first step in protecting your privacy and data integrity.

Measures to Prevent Unauthorized Opening of your iPhone
Prevention is always better than cure, especially when it comes to securing your personal electronic devices.
Setting a Secure and Complex Passcode
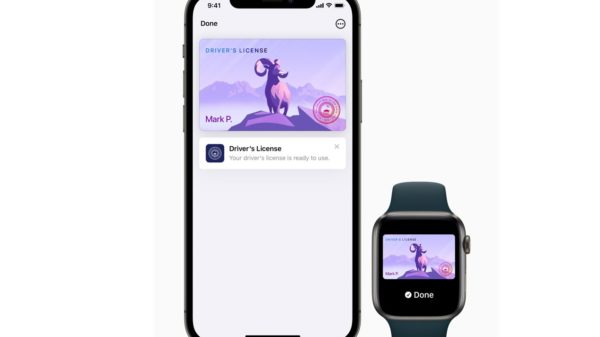
One fundamental security measure is the establishment of a strong, complex passcode. This is your first line of defense. Even if your device is physically opened, a secure passcode can help protect the data contained within your iPhone.
Regularly Updating iOS Software
Staying up-to-date with the latest iOS updates is also critical. These updates not only enhance your device’s functionality but more importantly, include the latest security patches to protect against unauthorized software modifications.
Choosing Authorized Service Providers
When it comes to repairs or servicing your iPhone, it is advisable to opt for authorized service providers. These professionals are obligated to follow strict guidelines set by the manufacturer and to respect customer privacy. Additionally, using authorized services ensures that your device’s warranty remains intact, providing peace of mind and security for your device in the long run.
Conclusion
Keeping your iPhone secure is an ongoing process that requires regular checks and conscious practices. This guide provides a comprehensive road map to determine if your iPhone has been opened without your authorization. Always remember to safeguard your device against unauthorized opening as it’s not just about data privacy but also about maintaining the iPhone’s functional integrity. The realization and understanding of the depth of the issue will guide you in making informed decisions, and prevent potential security breaches in the future.